When you first hear the word Steganography, you might roll your eyes and think, “great… sounds like more technical jargon!”.
However, to many people’s surprise, steganography has actually been around for centuries. It’s quietly prevalent all throughout society. In fact, everywhere you look online, you’d be hard-pressed not to find some remote example of steganography.
What is steganography and how does it work?
It’s the science of hiding information within another piece of information.
It is the derivative of the greek word steganos (meaning “covered”) and graphein (meaning “in writing”). The first cases of documented steganography involved carving a secret message into a wood tablet, and covering it with wax. Then a separate “decoy” message would be carved into the top layer of wax, so anyone who maliciously intercepted the tablet couldn’t see the underlying message being sent.
So what does this mean today?
In the last decade, an explosion of digital content worldwide has led to a massive need for improved security. There are countless loopholes allowing hackers to break into computers and maintain full access to all of their stored information. Also, with cryptocurrency slowly becoming mainstream, the importance of individual data security is growing significantly. Once inside a computer, a hacker can easily find important information — or anything else of value for that matter. It would be debilitating to have your private information intercepted or hard-earned money stolen by online thieves.
Examples of Steganography
What if your important files could be completely disguised as something else?
This is where steganography fits right in. Whether it’s data hidden in images, audio, or video files, there are now many different forms of hiding important digital information in plain sight. One of the most common forms is through the use of images. With a simple image file, you can even hide your private encrypted keys to a crypto wallet, making them completely invisible to anyone snooping around your computer.
With this method, a hacker could be staring right at your private keys, without even knowing it.
The thief would have to go through a very lengthy process of decoding every single image on your computer in hopes of finding the right one. A recent example of this key-to-image technique is this multi-million dollar bitcoin transaction that security expert Andreas Antonopoulos sent via an image of kittens playing in grass.
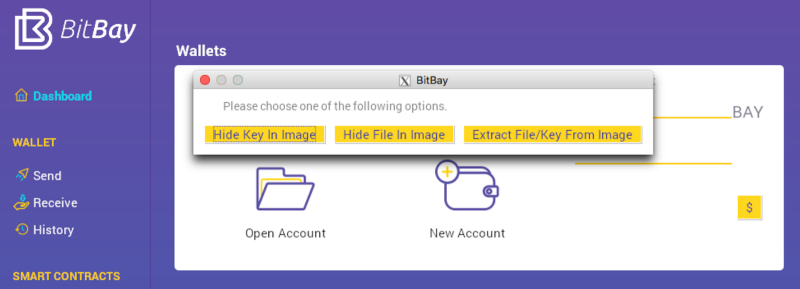
Here at BitBay, security is (and always has been) our top priority. We’ve added extensive layers of protection to our platform, including our very own seamlessly integrated steganography feature.
With a few simple mouse clicks, you can hide your private keys, contracts, or any other important files within any image of your choice. Our Market Client’s steganography feature opens the door to many different possibilities. You can quickly and discreetly send private information to friends or colleagues, and this feature also has the ability to extract and decrypt any files that are sent to you.
Just imagine, what if you could send an email containing important information, all in pictures?
With BitBay, that is now possible. If someone intercepts the message, or breaks into the email providers servers, they would only see a “useless” image. To take things a step further, you could also divide the sensitive information into multiple images, and send via multiple emails. When combined together, steganography and diversification create a powerful layer of security.
It’s our goal provide a vast array of options for our users — to protect and maintain the privacy of information that is most important to them. We the BitBay team, use this platform ourselves on a daily basis. In addition to the steganography feature, we’ve also built in many other security optionsincluding base-layer decentralization, encrypted communication (bitmessage), anonymity, anti-keylogger tool (for passwords), and much more.
The team at BitBay is dedicated our project’s development and success. We are a group of talented people all over the world, who work relentlessly around the clock to complete roadmap items ON TIME, EVERY TIME.
Want to check out our free contracting software and markets yourself?
Have feedback? Need support? Want to chat with a BitBay team member?
Feel free to join our growing community of users on our forum, here.
We’re always looking to improve our product, and your feedback is welcomed : )
Also, check out our roadmap for more exciting things coming soon!
